DDoS Attack Ransom Notes a Growing Menace for Businesses of All Sizes
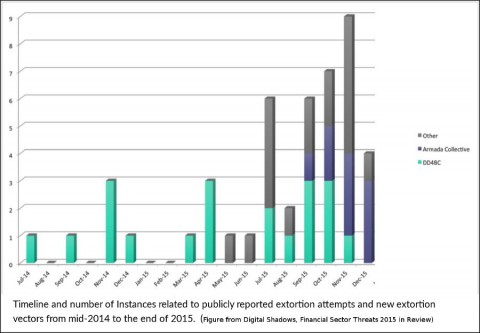
Reports of DDoS attacks—preceded by ransom notes—are surging, according to surveys conducted by IBM Security and Digital Shadows. This is alarming because, while a DDoS attack won’t destroy your data, it will still disrupt your business and result in significant expenses.
“It’s Extortion 2.0”, says Netcotech CEO Gideon Gideon, “These criminals are using black art cyber tools to extort money from innocent organizations, and they’re doing it anonymously and from a distance.”
Once the scourge of governments and large multinationals, more and more small and medium sized businesses across all sectors are seeing increases in these and other types of cyber attacks.
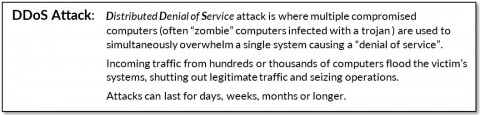
A few years ago, most DDoS attacks were either politically or protest motivated, dirty tricks from competitors, weapons of war by governments, or used to cloak other hacking attempts.
Cyber criminals have since learned that many smaller organizations will pay a fee of a few thousand dollars to avoid becoming victimized. Since it’s relatively easy to stage an attack, all they need to do is send out batches of Ransom Notes to pre-selected targets. After that the process is mostly automated.
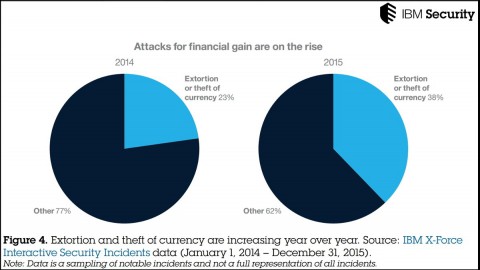
The number of reported cyber extortion or theft attempts reported by IBM Security increased by an alarming 40 percent over a two year period between 2014 and the end of 2015. This is surely because there is relatively easy money to gain, and little risk of getting caught.
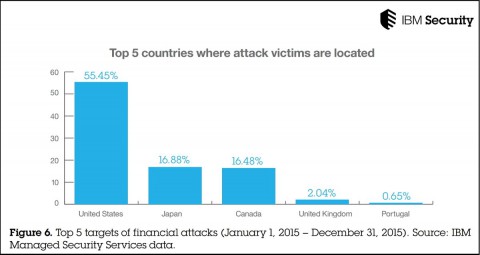
A large majority of DDoS attacks are still in the U.S., while Canadian organizations seem to be a pretty much tied for second place favourite with Japan.
Here’s an example of a recent ransom notes delivered by email:
“Subject: Ransom request: DDOS ATTACK!
FORWARD THIS MAIL TO WHOEVER IS IMPORTANT IN YOUR COMPANY AND CAN MAKE DECISION!
We are [Criminal Group].
All your servers will be DDoS-ed starting Friday if you don’t pay 2 Bitcoins @ [BITCOIN ADDRESS]
When we say all, we mean all – users will not be able to access sites host with you at all.
If you don’t pay by Friday, attack will start, price to stop will increase to 2 BTC and will go up 5 BTC for every day of attack.
How do I get Bitcoins?
You can easily buy bitcoins via several websites or even offline from a Bitcoin-ATM. We suggest you to start with localbitcoins.com<http://localbitcoins.com/> or do a google search.
What if I don’t pay?
If you decide not to pay, we will start the attack at the indicated date and uphold it until you do, there’s no counter measure to this, you will only end up wasting more money trying to find a solution. We will completely destroy your reputation amongst google and your customers and make sure your website will remain offline until you pay.
This is not a hoax, do not reply to this email, don’t try to reason or negotiate, we will not read any replies. Once you have paid we won’t start the attack and you will never hear from us again!
Please note that Bitcoin is anonymous and no one will find out that you have complied.
Just to be clear, these ransom notes are not the same as “Ransomware”, which we posted about earlier this year.
Ransomware is malicious code which encrypt disc drives, then ask payment for a key to unlock your data.
Usually the data is destroyed if payment is not received by some deadline.
The criminal motivations are the same though – receiving a financial reward for returning control of your own property to you. Also like Ransomware, the fee is usually small enough to make it easier—and cheaper—to pay them rather than suffer the consequences.
2 Bitcoins are currently worth about $920 U.S. Ransom demands have been seen as high as 20 Bitcoins, but most seem to range between 2 and 5 Bitcoins. Compared to the average loss of $500,000 for a mid-size organization, the ransom fee can seem like a small price to pay. And many do pay.
Also be aware that these Ransom Notes are threats. Some recent demands were not paid… and nothing happened. It seems that some attackers don’t really have the resources to follow through with their threats, you just never know. It’s that uncertainty that they’re counting on.
The Big Question: What should you do if your company receives a DDoS Ransom Note?
This is an important question, because as long as there are companies who will pay, this type of crime is going to continue accelerating in growth and in demands.
UNDER NO CIRCUMSTANCES SHOULD YOU EVER PAY THESE RANSOM NOTES.
There is no guarantee they will not attack if you pay them, and you are more likely to become a frequent victim after paying once. We all have a responsibility to make these extortion attempts as ineffective as possible.
Instead, use your money to ensure your network is as prepared as possible for a DDoS attack. Contact your Security Provider or ISP to see what they can do to help you.
Ensure your network systems and firewall are as secure as possible, and make sure your backups are current and safe in an offsite place. If possible, subscribe to a good DDoS mitigation service.
Be prepared that if a DDoS attack is going to happen, there’s often not a lot you can do to “stop” it. There are, however, things you can do to prepare your company beforehand that will help mitigate and minimize the impact to your company.
Watch this blog space for more on this topic
Next week we’ll publish more details about what to expect from a DDoS attack, and what steps you can do to mitigate and minimize the effects beforehand.